As part of CSCE 413, Software Security at Texas A&M, each student accomplished approximately 2-3 PoCs relating to various security concepts every week, including some short essays on popular viruses and vulnerabilities. These PoCs include, but are not limited to, OWASP top 10, Google Dorks, SQLi and XSS, rudementary MITM, network scanners and port knocking, Android vulnerabilities, buffer overflows, Metasploit, password cracking, and popular tooling.
What follows is a list of these PoC’s and their respective reports. Actual demo scripts can be provided upon request.
Reports & Downloads
PoC Report - Finding OWASP Vulnerabilities w/ Google Dorks
PoC Report - Performing an Authentication Bypass
PoC Report - Stored and Reflected XSS Injections
PoC Report - SQL Injections
PoC Report - MITM Attacks
PoC Report - Custom NMAP and Scanners
PoC Report - Port Knocking
PoC Report - Honeypots
PoC Report - APKs and Android Vulnerabilities
PoC Report - Buffer Overflows
PoC Report - Ret2Lib and Rop Chains
PoC Report - Shellcode
PoC Report - Metasploit Basics
PoC Report - Password Cracking
PoC Report - RNGs
PoC Report - Static Analysis Tools
PoC Report - Fuzzing
PoC Report - Symbolic Execution
PoC Report - Strace
PoC Report - Ltrace
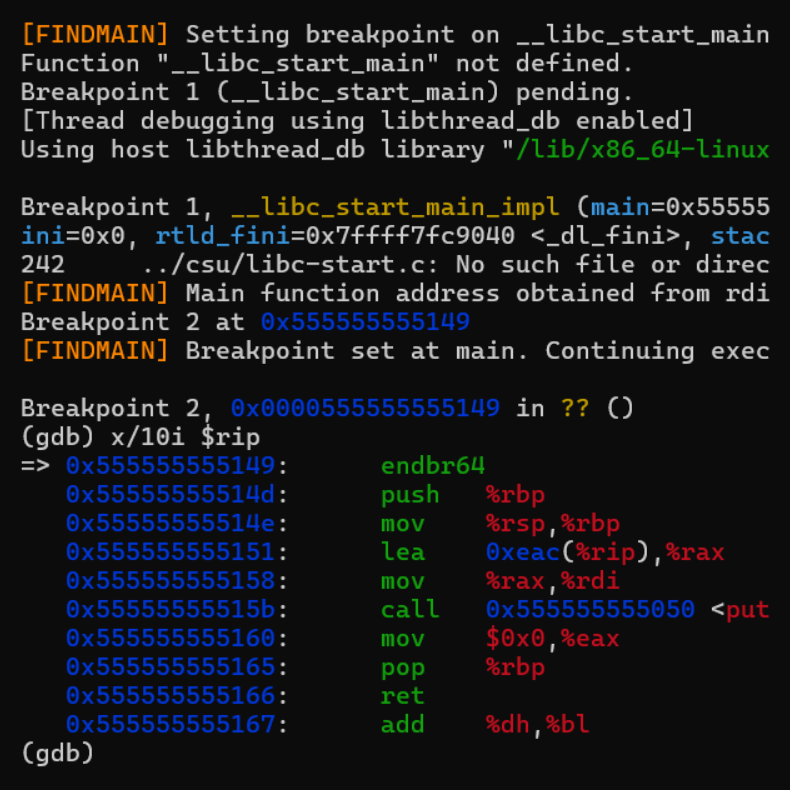
PoC Report - Custom GDB
PoC Report - Ptrace
PoC Report - Rootkits
Self Study - DirtyCow
Self Study - Eternal Blue
Self Study - GoToFail
Self Study - Heartbleed
Self Study - Meltdown
Self Study - PingOfDeath
Self Study - ShellShock
Self Study - Spectre
Self Study - WannaCry